Students can access the CBSE Sample Papers for Class 12 Computer Science with Solutions and marking scheme Term 2 Set 8 will help students in understanding the difficulty level of the exam.
CBSE Sample Papers for Class 12 Computer Science Term 2 Set 8 with Solutions
Maximum Marks: 35
Time: 2 hours
Instructions:
- The question paper is divided into 3 sections – A, B and C.
- Section A, consists of 7 questions (1-7). Each question carries 2 marks.
- Section B, consists of 3 questions (8-10). Each question carries 3 marks.
- Section C, consists of 3 questions (11-13). Each question carries 4 marks.
- Internal choices have been given for question numbers 7, 8 and 12.
Section – A
(Each question carries 2 Marks)
Question 1.
Give any two operations that are performed on data structure.
Answer:
Insertion It means addition of a new data element in a data structure.
Deletion It means removal of a data element from a data structure. The data element is searched before its removal.
![]()
Question 2.
(i) Expand the following
(a) SMTP
(b) HTML
Answer:
(a) SMTP – Simple Mail Transfer Protocol
(b) HTML – HyperText Markup Language
(ii) Which topology contains a backbone cable running through the whole length of the network?
Answer:
Bus topology
Question 3.
Explain any four constraints used in DBMS.
Answer:
There are some types of constraints are
- NOT NULL Constraint It ensures that a column cannot store NULL value.
- UNIQUE Constraint It is used to uniquely identify each record in a database.
- PRIMARY KEY Constraint It ensures that a column have a unique identity, which helps to find a particular record in a table and no column that is part of the primary key constraint can contain a NULL value.
- FOREIGN KEY Constraint It designates a column or combination of columns as a foreign key and establishes its relationship with a primary key in different tables.
Question 4.
A result is extracted from the database using the cursor object by giving the following statement.
d = cursor . fetcha 11 ( )
(i) How many records will be returned by fetchall() method?
Answer:
All records
(ii) What will be the datatype of object d after the given command is executed?
Answer:
List of tuples
Question 5.
Observe a table ITEM and give the output of following queries.
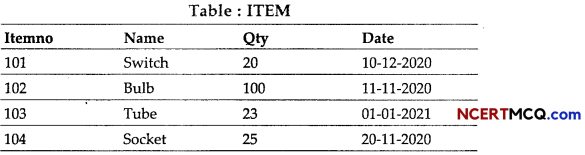
(i) SELECT SUM (Qty) FROM ITEM WHERE Name LIKE “S%;
Answer:
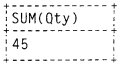
(ii) SELECT MAX (Qty) FROM ITEM;
Answer:
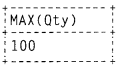
(iii) SELECT Itemno, Name FROM ITEM WHERE Qty < 50 AND Name LIKE “%u%”;
Answer:
![]()
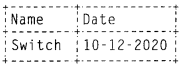
(iv) SELECT Name, Date FROM ITEM WHERE Date LIKE “%12%”;
Answer:
Question 6.
(i) Which component of database system consists of various secondary storage devices on which data is stored?
Answer:
Hardware
(ii) Which type of language of SQL provides statements for creation and deletion of the database tables, views?
Answer:
DDL (Data Definition Language)
Question 7.
Write answer the following questions, which are based on table PERSON given below.
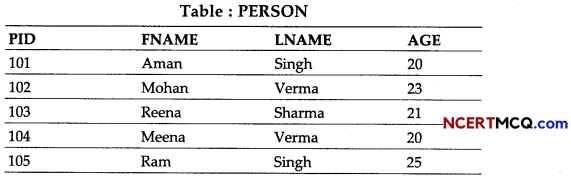
(i) What is cardinality and degree of a relation?
(ii) Display all the person record of age 18 to 22.
Or
(i) Alter table add CITY column in it as a type character.
(ii) Identify the candidate keys of table PERSON.
Answer:
(i) Cardinality – 5, Degree – 4
(ii) SELECT *FR0M PERSON WHERE AGE BETWEEN 18 AND 22;
Or
(i) ALTER TABLE PERSON ADD CITY CHAR(20);
(ii) PID, FNAME, LNAME
![]()
Section – B
(Each question carries 3 Marks)
Question 8.
Suppose STACK is allocated 6 memory locations and initially STACK is empty (Top = 0).
Give the output of the program segment.
AAA = 4 BBB = 6 Push (STACK, AAA) Push (STACK, 4) Push (STACK, BBB + 2) Push (STACK, AAA + BBB) Push (Top > 0): Element = STACK, pop ( ) print (Element)
Or
Write the Push operation of stack containing person names. Notice that the name should only accept characters, spaces and period (.) except digits. Assume that Pname is a class instance attribute.
Answer:
Output
10
10
8
4
4
Or
def insert():
name_pattern = re.compile (r “[A - Za - zs.]")
while True : n = input ("Enter name:”)
while name_pattern. search (n): :
print (“Invalid name”)
print (“Enter name correctly”)
n = input( )
Sname. append (n)
c = input (“Enter more name <y/n>”).upper ( )
if (c! = ‘y’):
break
![]()
Question 9.
(i) Write the syntax to add a column into a table using SQL command.
Answer:
ALTER TABLE table_name ADD
column_name datatype;
(ii) Explain the following SQL commands in brief.
(a) UPDATE
Answer:
UPDATE It is used to modify existing record in a table.
e.g. Change city value of a person to DELHI for PID 101.
UPDATE TABLE SET CITY=‘DELHI’
WHERE PID = 101;
(b) INSERT
Answer:
INSERT It is-used to insert new values in the existing table.
e.g. Add one row with values in a PERSON table.
INSERT INTO PERS0N(PID, FNAME, LNAME, AGE) VALUES(108, ‘Geeta’, ‘Sharma’, 23);
Question 10.
Create a database HUMAN in MySQL. Also, create a table PERSON with given constraints and data types for each column.
PID – Numeric and primary key, FNAME – Character max length 20, cannot be empty,
LNAME – Character max 20 length, AGE – Numeric and must be at least 18.
Answer:
CREATE DATABASE HUMAN;
CREATE TABLE PERSON (
PID INT,
FNAME CHAR(20) NOT NULL,
LNAME CHAR(20),
AGE INT, CHECK (AGE > = 18),
PRIMARY KEY(PID));
![]()
Section C
(Each question carries 4 Marks)
Question 11.
Consider the following tables STUDENT and STREAM. Write SQL commands for the statements (i) to (iv).
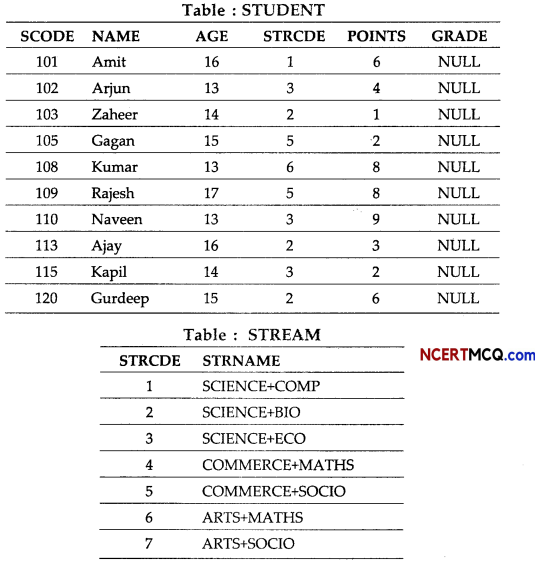
(i) To display the name of streams in alphabetical order from table STREAM.
Answer:
SELECT STRNAME FROM STREAM ORDER BY STRNAME;
(ii) To display the number of students whose POINTS are more than 5.
Answer:
SELECT COUN(*) FROM STUDENT WHERE POINTS > 5;
(iii) To update GRADE to A’ for all those students, who are getting more than 8 as POINTS.
Answer:
UPDATE STUDENT SET GRADE = ‘A’ WHERE POINTS > 8;
(iv) ARTS+MATHS stream is no more available. Make necessary change in table STREAM.
Answer:
DELETE FROM STREAM WHERE STRNAME = ‘ARTS + MATHS’;
Question 12.
(i) Explain FTP and telnet network protocols in brief.
Or
Define terms – internet and intranet.
Answer:
FTP The File Transfer Protocol is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network. FTP is built on a client-server model architecture using separate control and data connections between the client and the server.
Telnet This is also called as Remote login. It is used to make connection between remote computers. After establishment of connection with remote host, the telnet client becomes a virtual terminal. It provides an error free connection.
Or
Internet Internet is a called as network of networks, where many networks are connected together to make a big worldwide network, which can be accessed by the general public, anywhere anytime. The network connected can be related with business, finance, game, education, etc. These network can share their data, information, documents on the networks using WWW.
Intranet This type of network belongs to only one organisation. Means if the devices of one organisation are connected with each other with an objective to share data with each other then it is called as Intranet.
![]()
(ii) Answer the following
(a) Write any two benefits of using computer network.
(b) What do you mean by data transfer rate?
Answer:
(a) Two benefits of using computer network are
- File Sharing Computer network helps connected user is sharing of data and files with each other.
- User Communication Connected user can send and receive messages with each other, using email, chat or other applications of messaging.
(b) Data Transfer Rate Data travels in the form of signals over a channel. One signal carries one or more bits over the channel. Data transfer rate is the number of bits transmitted between source and destination in one second. It is also known as bit rate. It is measured in terms of bits per second (bps).
Question 13.
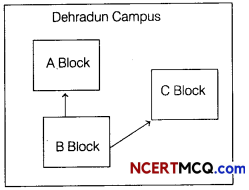
A School in Dehradun has three blocks A, B and C. It is required to setup a network in the school. The head office of the school is in Delhi.
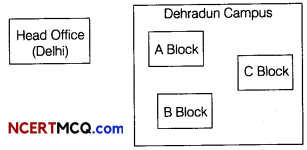
Distance between blocks are as follows
A to C – 100m
A to B – 40m
B to C – 55m
Dehradun Campus to Delhi Head Office – 350km
Number of computers installed at each building
| A | 15 |
| B | 100 |
| C | 30 |
| Head Office | 10 |
(i) Suggest most suitable place to install a server.
Answer:
Most suitable building is B block to install a server because it has maximum number of computers.
![]()
(ii) Suggest a layout to connect these blocks for wired channel in Dehradun campus.
Answer:
(iii) Suggest placement of switch device in network.
Answer:
Switch needs in every building as they help in sharing of bandwidth.
(iv) The School is planning to make an admission office in Chandigarh far from approximately 300 km, which type of network will be formed (LAN, MAN, WAN)?
Answer:
WAN will be the network as the distance is beyond LAN or MAN.